1.4.17.4: Information Networks
- Last updated
- Save as PDF
- Page ID
- 58616
What you’ll learn to do: compare the ways that businesses can manage information
Billions and billions of bits of data flood into an organization’s information system, but how does that data get utilized effectively? The challenge lies not so much with the collection or storage of the data: today, it is possible to collect and even store vast amounts of information relatively cheaply. The main difficulty is figuring out the best and most efficient way to extract and manage the relevant data and resulting information. In this section you will learn how organizations use a variety of networks to manage their information.
Learning Objectives
- Discuss how businesses can use intranets and extranets to manage information
- Discuss how businesses can use Virtual Private Networks (VPNs) to manage information
The Internet and Cloud Computing
Once it’s grown beyond just a handful of employees, an organization needs a way of sharing information. Imagine a flower shop with twenty employees. The person who takes phone orders needs access to the store’s customer list, as do the delivery person and the bookkeeper. Now, the store may have one computer and everyone could share it. It’s more likely, however, that there are a number of computers (several for salespeople, one for delivery, and one for bookkeeping). In this case, everyone needs to be sure that customer records have been updated on all computers every time that a change is required. Traditionally the business would install a network (LAN) to allow the various computers to talk to one another and share information. Today businesses are looking to the cloud to provide a network solution.
Cloud Computing
So, what is cloud computing? Watch the following video, which describes some of the uses and benefits of cloud computing.
The term “cloud computing” means performing computer tasks using services provided over the Internet. In cloud computing a company’s data and applications are stored at an offsite data center that is then accessed via the Internet (the cloud). So when you hear or read that an individual or company is using the “cloud” or technology firms, such as IBM, Hewlett-Packard, and Salesforce.com, are offering cloud services, just substitute the word “Internet” for “cloud” and things will make sense.
You might be surprised to learn that you’re already using the cloud—that is if you use Facebook (which is very likely—in fact, just mentioning Facebook here might prompt you to stop studying and check out your friends’ pages). How do you know that Facebook is a cloud application? Remember the trick: just substitute the word “Internet” for “cloud.” The Facebook computer application lets you store information about yourself and share it with others using the Internet.
practice question \(\PageIndex{1}\)
How do businesses use the Internet to manage information?
- Businesses use cloud (Internet) computing as the primary way to manage their information
- Businesses can use the internet to send and receive email.
- Businesses can use the Internet to host their accounting systems
- Businesses can use the internet to track customer activity
- Answer
-
a. Cloud Computing offers businesses both functionality (applications and storage) as well as connectivity (a network to allow access to the applications and stored data).
Advantages and Disadvantages of Cloud Computing
In making a decision whether or not to use cloud computing to store and share information, a business should consider some of its advantages and disadvantages.
Advantages
- Cost Savings—By “renting” software rather than buying it the cloud can reduce. In most instances, the monthly fee to “use” software is generally less than the combined cost of buying, installing, and maintaining the software internally. On the hardware site, housing data in a service provider’s facilities (such as Amazon or Google), rather than in-house, reduces the large outlay of cash needed to build and maintain data centers.
- Speed of Delivery—Purchasing and installing software and data processing equipment can be time consuming. A cloud computing service provider can get applications up and running in a minimal time frame and often without interrupting normal business operations.
- Scalable— As businesses grow it’s often difficult to gauge the level of technology needs. If businesses overestimate their requirements, they end up paying for technology they don’t need. If they underestimate, efficiency goes down, and the experience for customers may diminish. By using cloud computing businesses are able to have exactly what they need at their disposal at any point in time.
- Employees Can Be Mobile—The use of cloud computing frees workers from their desks and allows them to work wherever they are. As applications move to the cloud, all that is needed for employees to connect to their “offices” is the Internet. This mobility benefit also makes it easier for employees to collaborate on projects and connect with others in the company.
- Information Technology Staff— Finding experienced and knowledgeable information technology staff is a continuing problem for many businesses. By using cloud computing, businesses can reduce their human resource needs by shifting some of the work to outside vendors who have a staff of highly skilled individuals.
Disadvantages
Although the advantages of moving to a cloud environment outnumber the disadvantages, the following disadvantages are cause for concern:
- Disruption in Internet Service— Since both applications and data are accessed via the Internet, if the Internet is unavailable because of a disruption this could create serious problems for a business.
- Security—Many companies are reluctant to trust cloud service providers with their data because they’re afraid it might become available to unauthorized individuals or criminals. This is a particular concern to business that collect and store sensitive client information.
- Service Provider System Crash—Organizations considering moving to the cloud are often concerned about the possibility of a computer service crash at their service providers’ facilities. If the service provider experiences an outage, then the business is in effect cut off from its data and operations.
Although there are some disadvantages, using cloud computing to manage information is the new normal for many businesses. In fact, according to Forbes magazine, the cloud computing market is estimated to grow to $411 billion by 2020. The global cloud computing services market size is driven by many factors. The most important factor, which is driving the market, is the cost effectiveness. With the deployment of cloud computing services, organizations can save more than 35% of the annual operating costs of their information systems. Clearly the future for the cloud is sky high!
Intranets and Extranets
Intranets
Increasingly, businesses are relying on intranets to deliver tools such as collaboration, scheduling, customer relationship management tools, and project management to increase the productivity of the organization. An intranet is a private network accessible only to an organization’s staff. Unlike the Internet, an internal intranet provides a wide range of information and services to employees of an organization but these tools and information are unavailable to the public. A company-wide intranet is an important focal point of internal communication and collaboration, and can provide a business with a single starting point to access both internal and external resources. Larger businesses allow users within their intranet to access the public Internet through firewall servers. Because businesses have the ability to screen both incoming and outgoing traffic, they are able to keep the security of the intranet intact. In its simplest form, an intranet is established with the technologies for local area networks (LANs) and wide area networks (WANs).
Some of the advantages and benefits a company can realize from establishing a robust intranet are as follows.
- Workforce productivity. Intranets can help users to locate and view information faster and use applications relevant to their roles and responsibilities.
- Enhanced collaboration. Information is easily accessible by all authorized users, which enables teamwork. Being able to communicate in real-time through integrated third party tools promotes the sharing of ideas and helps boost a business’ productivity
- Time Savings. Intranets allow organizations to distribute information to employees on an as-needed basis in real time. Employees may link directly to relevant information as soon as the organization makes it available on the intranet.
- Reduced Costs. Users can view information and data via web-browser rather than maintaining physical documents such as procedure manuals, internal phone list and requisition forms. This can potentially save the business money on printing, duplicating documents, and the environment as well as document maintenance overhead.
- Improved Communication. Intranets can serve as powerful tools for communication within an organization. A great real-world example of where an intranet helped a company communicate is when Nestle had a number of food processing plants in Scandinavia. Their central support system had to deal with a large number of requests for information every day. When Nestle decided to invest in an intranet, they quickly realized the savings. In fact, the savings from the reduction in calls was substantially greater than the investment in the intranet[1].
Extranets
In some cases organizations make the decision to allow external parties such as customers and suppliers to have access to their intranet. When these outside parties are provided access to a subset of the information accessible from an organization’s intranet the intranet becomes an extranet. For example a large construction company may share drawings with architects or inspectors, photographs to their customers and loan documents to their bankers by implementing online applications that allow these external parties to access and even mark-up and make changes to documents. In essence, the company will use an extranet to manage project-related communications. One of the biggest advantages of establishing an extranet is that a business can share large quantities of data using EDI or electronic data interchange. Data such as invoice and order that were traditionally transmitted via paper can now instantly be shared among organizations. Some of the most sophisticated extranets are run by large retailers like Walmart and Target who constantly transmit data via their extranet to vendors and suppliers, ensuring that merchandise arrives when it is needed, where it is needed.
Like intranets, extranets have some distinct advantages for the organizations establishing them. Several of these benefits are explained below.
- Build customer relationships. Customers who are provided access to timely information about product availability, specifications and cost increase their efficiency. In business-to-business relationships, the more timely and accurate information a business makes available to their customers, the more likely they are to retain that business. Collaborate with other companies on joint development efforts
- Reduced margin of error. An extranet can reduce a company’s margin of error thereby reducing or eliminating costly errors, especially with something as complex as processing orders from distributors and suppliers. Customers can be given access to their accounts to verify order history, account balances and payments.
- Timely and accurate information. On an extranet a business can instantly change, edit, and update sensitive information such as price lists or inventory information. Compared to typical paper-based publishing processes, an extranet offers a unique opportunity to quickly get information into the right hands before it’s out-of-date.
- Reduced inventory. One of the greatest advantage of a business-to-business extranet is its impact on supply-chain management. By linking the inventory system directly to a supplier, businesses can process orders as soon as the system knows they are needed, thus reducing the stock a business keeps on hand and generally making the procurement process more efficient.
- Flexibly. A well designed extranet allows remote and mobile staff to access core business information 24 hours a day, irrespective of location. This allows employees to work remotely or respond to critical requests for information after normal working hours. As businesses expand globally, the ability to work across time zones is enhanced by the establishment of an extranet.
practice question \(\PageIndex{2}\)
What is the primary difference between how businesses use intranets versus extranets?
- Intranets are secret networks used only by insiders while extranets are wide-open to the public
- Intranets are networks for the use of internal employees only, while extranets allow customers and partners access to the network
- Intranets utilize LAN and WAN technology while extranets only use LAN technology.
- Businesses use both intranets and extranets to develop information about their competitors.
- Answer
-
b. The primary difference between intranets and extranets is who has access to the network.
Whether a company is managing an intranet or extranet, both systems can raise security issues. With increased access comes an increased opportunity for security breaches. In particular, the security of extranets can be a concern when hosting valuable or proprietary information. Unless sufficient security precautions are taken, data can be breached and altered, without either the sender or the receiver being aware of the interception. The growth in the complexity of networks has increased the possible points of attack, both from within organizations and from outside the company. Fortunately, the means of protecting against hackers have also expanded in line with the technology.
Virtual Private Networks (VPNs)
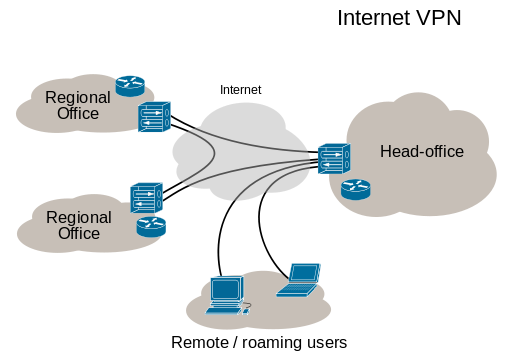
A virtual private network (VPN) extends a private network (intranet) across a public network Internet), and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. Applications running across a VPN may therefore benefit from the functionality, security, and management of the private network while taking advantage of the flexibility of the Internet. In a business setting, remote-access VPNs allow employees to access their company’s intranet from home or while traveling outside the office. Site-to-site VPNs allow employees in geographically separated offices to share one cohesive virtual network.
To ensure security, the VPN connection is established using encryption protocols and VPN users use authentication methods, including passwords or certificates, to gain access to the VPN.
Although VPNs cannot make online connections completely secure, they can increase privacy and security. For example, to prevent disclosure of private information, VPNs typically allow only authenticated remote access using encryption techniques.
Some of the security advantages of a VPN include the following:
- even if the network traffic is accessed, an attacker would see only encrypted data
- sender authentication is required to prevent unauthorized users from accessing the VPN
- the VPN messaging is designed to detect instances of tampering with transmitted messages
As security concerns continue to grow in the digital age, more and more companies are emerging to serve the growing demand for VPN services. Which service a business chooses will be determined by its planned uses for the VPN.
practice question \(\PageIndex{3}\)
How do businesses utilize Virtual Private Networks (VPN) to manage information?
- VPNs provide Video Protected Networks to allow companies to host video conferences world-wide
- VPNs provide remote server backups and archives to protect company data
- VPNs provide external secure access to internal networks via the internet so that remote users can be productive despite geographical location.
- VPNs block external access to sensitive internal networks in order to guarantee information safety.
- Answer
-
d. VPNs provide both access and security across multiple locations.
- McGovern, Gerry (November 18, 2002). "Intranet return on investment case studies".. Retrieved 2018-11-03 ↵

