17.1: THE STRUCTURE OF THE JUVENILE JUSTICE SYSTEM
- Page ID
- 66386
CHAPTER 17 - JUVENILLE JUSTICE
THE STRUCTURE OF THE JUVENILE JUSTICE SYSTEM [163]
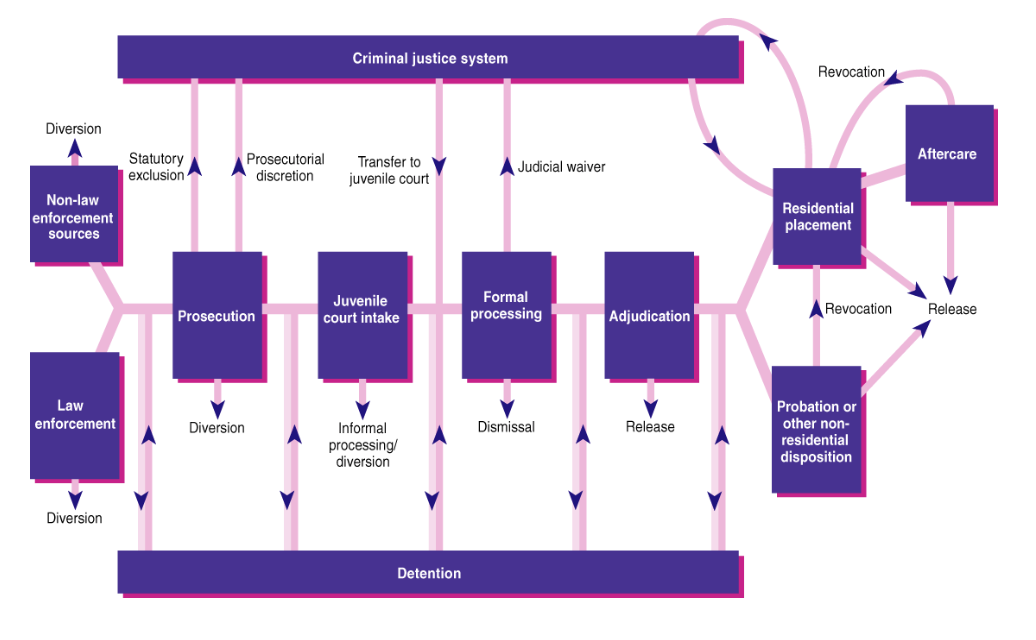
The juvenile justice system is used to handle cases in which minors are convicted of criminal offences, using early intervention in delinquency cases to discourage future adult criminal behavior. The juvenile justice process involves nine major decision points: (1) arrest, (2) referral to court, (3) diversion, (4) secure detention, (5) judicial waiver to adult criminal court, (6) case petitioning, (7) delinquency finding/adjudication, (8) probation, and (9) residential placement, including confinement in a secure correctional facility (see Juvenile Justice Process flow chart).
The majority of cases are first referred to the juvenile justice system through contact with police. Probation officers, school officials, or parents usually refer to the remaining cases. The most common offenses referred to court are property offenses (roughly 92%), followed by person offenses (89.5%), drugs (88.2%), and general delinquency charges (81.6%). Other referrals come from schools, family, or social workers or probation officers.
At the intake stage, probation officers or attorneys determine whether or not the case needs the attention of the juvenile court or if it can be handled informally, such as diversion to probation or a drug treatment program. If the case progresses to court, the authorities need to determine if the youth can be released to a parent/guardian or if the youth needs to be held in a secure detention center. When determining this, the court needs to assess the risk the youth poses to society and if the youth poses a flight risk. In some cases, the parent cannot be located or, if located, refuses to take custody of the youth. In these cases, the juvenile is remanded to custody. The decision to detain or release the juvenile will be made by the judge at a detention hearing.
If the case is handled in court, the county attorney needs to file a petition. When the youth has a formal hearing, it is called an adjudication rather than a trial in adult court. The adjudication of youth as delinquent can result in either dismissal of the charges or confinement at a secure institution. In most juvenile cases, the least restrictive option is usually sought, so the youth is usually put on probation or some sort of community treatment. Formal processing is less common than informal processing involving diversion or community-based programming.
|
|
Think About It… Working with Youth When I graduated from college with a BA in psychology, I applied for a job working with the Division of Youth Corrections in Denver, CO. I worked in a Residential Treatment Facility (RTC), which used behavior modification techniques, assigned caseworkers to each youth and their families, and attempted to help the kids learn problem-solving skills and accountability. Youth were confined for a variety of reasons, from committing gang affiliated drive-by shootings, to youth who were designated dependent youth through social services and had nowhere else to go. We had high-risk kids, low-risk kids, conduct disorder and mental health kids all together on the same unit. Having the mix of all these different kids is not a great formula; the low-risk kids learn negative behavior from the high-risk kids, and the conduct disorder kids victimize the mental health kids. In an ideal institution, these different populations would all be on separate units. Working with youth is hard. They push boundaries, are angry, try to manipulate those around them, and reject authority. However, working with youth is exceptionally rewarding. They are kids. They come from abusive and neglectful homes and are yearning for approval and love. For example, one boy in our facility was named Josh. He was a super angry and violent sixteen-year-old who was sentenced for committing aggravated assault. Through working with counselors and caseworkers, we discovered his anger was hiding immense sadness. He lashed out at those around him when he was sad because he had no way to show his feeling other than through aggression. Many months of working with him, encouraging him to journal, express his feelings, talk with others, use other tools to help him with his sadness led to amazing results. He left our facility after more than a year, graduated from high school and even went to college! Getting the individualized attention helped Josh change. He became a success story of the juvenile justice system. Working with youth takes patience, consistency, and compassion. It is one of the most difficult jobs there is, but it is possible to be a very positive influence in the lives of kids who need it the most. If you are interested in working with youth, plan on committing to at least a year. Incarcerated kids are used to having people give up on them and disappoint them, so you do not want to add to their negative experiences. Show up, follow through, and be optimistic about a better future for justice-involved youth. |
|
|
Pin It! In re Gault (1967) [165] Gerald “Jerry” Gault, a 15-year-old Arizona boy, was taken into custody for making obscene calls to a neighbor’s house. After the neighbor, Mrs. Cook filed charges, Gault and his friend were taken to the Juvenile Detention Home. At the time he was taken into custody, his parents were at work and the arresting officers made no effort to contact them nor did they leave a note about the arrest or where they were taking their son. They finally learned of his whereabouts from the family of the friend who was arrested with him. When the habeas corpus hearing was held two months later, Mrs. Cook was not present, no one was sworn in prior to testifying, and no notes were taken. He was released and scheduled to reappear a few months later for an adjudication hearing. In the following hearing, again, Mrs. Cook was not present and again, no official transcripts of the proceeding were taken. The official charge was “making lewd phone calls.” The maximum penalty for an adult charge with this was a $50 fine or not more than two months in jail. Gault was found guilty and sentenced to 6 years in juvenile detention. Gault’s parents filed a writ of habeas corpus which was eventually heard by the Supreme Court. The Supreme Court ruled that juveniles are entitled to due process rights when the court proceedings may result in confinement to a secure facility. The specific due process rights highlighted in this case include (1) fair notice of charges; (2) right to counsel; (3) right to confront and cross-examine witnesses; and (4) privilege against self-incrimination. The Court held that the Due Process Clause of the Fourteenth Amendment applies to juvenile defendants as well as adult defendants. “Juvenile court history has again demonstrated that unbridled discretion, however benevolently motivated, is frequently a poor substitute for principle and procedure.” |
PREVENTING DELINQUENCY [166]
|
Learning Objective |
|
|
Learning Objective: Key Points |
|
|
Learning Objective: Key Terms |
|
JUVENILE DELINQUENCY
Juvenile delinquency is participation in illegal behavior by minors. Most legal systems prescribe specific procedures for dealing with juveniles, such as juvenile detention centers and courts. A juvenile delinquent is a person who is typically under the age of 18 and commits an act that would have otherwise been charged as a crime if the minor was an adult. Depending on the type and severity of the offense committed, it is possible for persons under 18 to be charged and tried as adults.
Juvenile delinquency can be separated into three categories:
- Delinquency: crimes committed by minors that are dealt with by the juvenile courts and justice system;
- Criminal behavior: crimes dealt with by the criminal justice system;
- Status offenses: offenses which are only classified as such because one is a minor, such as truancy, also dealt with by the juvenile courts.
Young men disproportionately commit juvenile delinquency. Feminist theorists and others have examined why this is the case. One suggestion is that ideas of masculinity may make young men more likely to offend. Being tough, powerful, aggressive, daring, and competitive becomes a way for young men to assert and express their masculinity. Alternatively, young men may actually be naturally more aggressive, daring, and prone to risk-taking. According to a study led by Florida State University criminologist Kevin M. Beaver, adolescent males who possess a certain type of variation in a specific gene are more likely to flock to delinquent peers. The study, which appeared in the September 2008 issue of the Journal of Genetic Psychology, is the first to establish a statistically significant association between an affinity for antisocial peer groups and a particular variation (called the 10-repeat allele) of the dopamine transporter gene (DAT1).
There is also a significant skew in the racial statistics for juvenile offenders. When considering these statistics, which state that Black and Latino teens are more likely to commit juvenile offenses, it is important to keep the following in mind: poverty is a large predictor of low parental monitoring, harsh parenting, and association with deviant peer groups, all of which are in turn associated with juvenile offending. The majority of adolescents who live in poverty are racial minorities.
Family factors that may have an influence on offending include:
- the level of parental supervision,
- the way parents discipline a child,
- particularly harsh punishment,
- parental conflict or separation,
- criminal parents or siblings,
- parental abuse or neglect,
- the quality of the parent-child relationship.
Delinquency prevention is the broad term for all efforts aimed at preventing youth from becoming involved in criminal or other antisocial activity. Because the development of delinquency in youth is influenced by numerous factors, prevention efforts need to be comprehensive in scope. Prevention services may include activities like substance abuse education and treatment, family counseling, youth mentoring, parenting education, educational support, and youth sheltering. Increasing availability and use of family planning services, including education and contraceptives, helps to reduce unintended pregnancy and unwanted births—which are risk factors for delinquency.
Juvenile Delinquency : Juvenile delinquency refers to antisocial or illegal behavior by children or adolescents, for dealing with juveniles, such as juvenile detention centers. There are a multitude of different theories on the causes of crime, most if not all of which can be applied to the causes of youth crime.
TERRORISM [168]
Terrorism is an act of violence intended to create fear, which is then leveraged in order to achieve goals.
|
Learning Objective |
Criticize an instance in history in which the term “terrorist” or “terrorism” has been misused to describe a religious group, government, or revolutionary action, using the definition of terrorism in this text |
|
Learning Objective: Key Points |
|
|
Learning Objective: Key Terms |
|
Terrorism is the systematic use of terror, especially as a means of coercion. Although the term lacks a universal definition, common definitions of terrorism refer to violent acts intended to create fear (terror). These acts are perpetrated for a religious, political, or ideological goal, and deliberately target or disregard the safety of non-combatants (civilians).
Terrorism has been practiced by a broad array of political organizations for furthering their objectives. It has been practiced by right-wing and left-wing political parties, nationalistic groups, religious groups, revolutionaries, and ruling governments. An abiding characteristic is the indiscriminate use of violence against noncombatants to gain publicity for a group, cause or individual. Therefore, the power of terrorism comes from its ability to leverage human fear to help achieve these goals.
DEFINING TERRORISM [169]
There is an old saying that “one person’s freedom fighter is another person’s terrorist.” This saying indicates some of the problems in defining terrorism precisely. Some years ago, the Irish Republican Army (IRA) waged a campaign of terrorism against the British government and its people as part of its effort to drive the British out of Northern Ireland. Many people in Northern Ireland and elsewhere hailed IRA members as freedom fighters, while many other people condemned them as cowardly terrorists. Although most of the world labeled the 9/11 attacks as terrorism, some individuals applauded them as acts of heroism. These examples indicate that there is only a thin line, if any, between terrorism on the one hand and freedom fighting and heroism on the other hand. Just as beauty is in the eyes of the beholder, so is terrorism. The same type of action is either terrorism or freedom fighting, depending on who is characterizing the action.
Although dozens of definitions of terrorism exist, most take into account what are widely regarded as the three defining features of terrorism: (a) the use of violence; (b) the goal of making people afraid; and (c) the desire for political, social, economic, and/or cultural change. A popular definition by political scientist Ted Robert Gurr (1989, p. 201) captures these features: “The use of unexpected violence to intimidate or coerce people in the pursuit of political or social objectives.”

As the attacks on 9/11 remind us, terrorism involves the use of indiscriminate violence to instill fear in a population and thereby win certain political, economic, or social objectives.
TERRORISTS
The terms “terrorism” and “terrorist” carry strong negative connotations. These terms are often used as political labels to condemn such violence as immoral, indiscriminate, or unjustified or to condemn an entire segment of a population. However, some groups, when involved in a liberation struggle, have been called terrorists by the Western governments or media. In some liberation struggles, these same persons can become the leaders or statesman of these liberated nations. Thus, the perpetrators of terrorism can widely vary; terrorists can be individuals, groups or states. According to some definitions, clandestine or semi-clandestine state actors may also carry out terrorist acts outside the framework of a state of war.


The 9/11 attacks spawned an immense national security network and prompted the expenditure of more than $3 trillion on the war against terrorism.
Terrorism is hardly a new phenomenon, but Americans became horrifyingly familiar with it on September 11, 2001. The 9/11 attacks remain in the nation’s consciousness, and many readers may know someone who died on that terrible day. The attacks also spawned a vast national security network that now reaches into almost every aspect of American life. This network is so secretive, so huge, and so expensive that no one really knows precisely how large it is or how much it costs (Priest & Arkin, 2010). However, it is thought to include 1,200 government organizations, 1,900 private companies, and almost 900,000 people with security clearances (Applebaum, 2011). The United States has spent an estimated $3 trillion since 9/11 on the war on terrorism, including more than $1 trillion on the wars in Iraq and Afghanistan whose relevance for terrorism has been sharply questioned. Questions of how best to deal with terrorism continue to be debated, and there are few, if any, easy answers to these questions.
Not surprisingly, sociologists and other scholars have written many articles and books about terrorism. This section draws on their work to discuss the definition of terrorism, the major types of terrorism, explanations for terrorism, and strategies for dealing with terrorism. An understanding of all these issues is essential to make sense of the concern and controversy about terrorism that exists throughout the world today.
TYPES OF TERRORISM
When we think about this definition, 9/11 certainly comes to mind, but there are, in fact, several kinds of terrorism—based on the identity of the actors and targets of terrorism—to which this definition applies. A typology of terrorism, again by Gurr (1989), is popular: (a) vigilante terrorism, (b) insurgent terrorism, (c) transnational (or international) terrorism, and (d) state terrorism. Table 17.1 “Types of Terrorism” summarizes these four types.
Table 17.1 Types of Terrorism
|
Type of Terrorism |
Definition |
|
Vigilante terrorism |
Violence committed by private citizens against other private citizens. |
|
Insurgent terrorism |
Violence committed by private citizens against their own government or against businesses and institutions seen as representing the “establishment.” |
|
Transnational terrorism |
Violence committed by citizens of one nation against targets in another nation. |
|
State terrorism |
Violence committed by a government against its own citizens. |
Vigilante terrorism is committed by private citizens against other private citizens. Sometimes the motivation is racial, ethnic, religious, or other hatred, and sometimes the motivation is to resist social change. The violence of racist groups like the Ku Klux Klan was vigilante terrorism, as was the violence used by white Europeans against Native Americans from the 1600s through the 1800s. What we now call “hate crime” is a contemporary example of vigilante terrorism.
Insurgent terrorism is committed by private citizens against their own government or against businesses and institutions seen as representing the “establishment.” Insurgent terrorism is committed by both left-wing groups and right-wing groups and thus has no political connotation. US history is filled with insurgent terrorism, starting with some of the actions the colonists waged against British forces before and during the American Revolution, when “the meanest and most squalid sort of violence was put to the service of revolutionary ideals and objectives” (Brown, 1989, p. 25). An example here is tarring and feathering: hot tar and then feathers were smeared over the unclothed bodies of Tories. Some of the labor violence committed after the Civil War also falls under the category of insurgent terrorism, as does some of the violence committed by left-wing groups during the 1960s and 1970s. A relatively recent example of right-wing insurgent terrorism is the infamous 1995 bombing of the federal building in Oklahoma City by Timothy McVeigh and Terry Nichols that killed 168 people.
Transnational terrorism is committed by the citizens of one nation against targets in another nation. This is the type that has most concerned Americans at least since 9/11, yet 9/11 was not the first time Americans had been killed by international terrorism. A decade earlier, a truck bombing at the World Trade Center killed six people and injured more than 1,000 others. In 1988, 189 Americans were among the 259 passengers and crew who died when a plane bound for New York exploded over Lockerbie, Scotland; agents from Libya were widely thought to have planted the bomb. Despite all these American deaths, transnational terrorism has actually been much more common in several other nations: London, Madrid, and various cities in the Middle East have often been the targets of international terrorists.
State terrorism involves violence by a government that is meant to frighten its own citizens and thereby stifle their dissent. State terrorism may involve mass murder, assassinations, and torture. Whatever its form, state terrorism has killed and injured more people than all the other kinds of terrorism combined (Gareau, 2010). Genocide, of course is the deadliest type of state terrorism, but state terrorism also occurs on a smaller scale. As just one example, the violent response of Southern white law enforcement officers to the civil rights protests of the 1960s amounted to state terrorism, as officers murdered or beat hundreds of activists during this period. Although state terrorism is usually linked to authoritarian regimes, many observers say the US government also engaged in state terror during the nineteenth century, when US troops killed thousands of Native Americans (D. A. Brown, 2009).
|
|
Pin It! Religious Terrorism Religious terrorism is performed by groups or individuals, the motivation of which is typically rooted in faith-based tenets. Terrorist acts throughout the centuries have been performed on religious grounds with the hope to either spread or enforce a system of belief, viewpoint or opinion. Religious terrorism does not in itself necessarily define a specific religious standpoint or view, but instead usually defines an individual or group interpretation of that belief system ‘s teachings. |
EXPLAINING TERRORISM
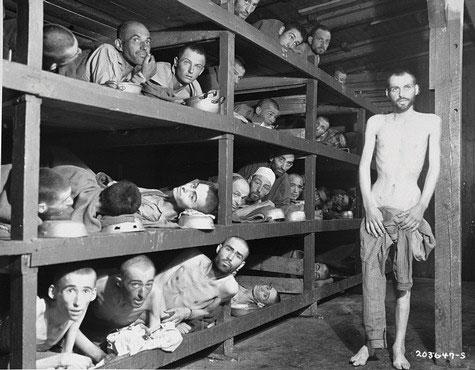
Genocide is the deadliest type of state terrorism. The Nazi holocaust killed some 6 million Jews and 6 million other people.
Why does terrorism occur? It is easy to assume that terrorists must have psychological problems that lead them to have sadistic personalities, and that they are simply acting irrationally and impulsively. However, most researchers agree that terrorists are psychologically normal despite their murderous violence and, in fact, are little different from other types of individuals who use violence for political ends. As one scholar observed, “Most terrorists are no more or less fanatical than the young men who charged into Union cannon fire at Gettysburg or those who parachuted behind German lines into France. They are no more or less cruel and coldblooded than the Resistance fighters who executed Nazi officials and collaborators in Europe, or the American GI’s ordered to ‘pacify’ Vietnamese villages” (Rubenstein, 1987, p. 5).
Contemporary terrorists tend to come from well-to-do families and to be well-educated themselves; ironically, their social backgrounds are much more advantaged in these respects than are those of common street criminals, despite the violence they commit.
If terrorism cannot be said to stem from individuals’ psychological problems, then what are its roots? In answering this question, many scholars say that terrorism has structural roots. In this view, terrorism is a rational response, no matter how horrible it may be, to perceived grievances regarding economic, social, and/or political conditions (White, 2012). The heads of the US 9/11 Commission, which examined the terrorist attacks of that day, reflected this view in the following assessment: “We face a rising tide of radicalization and rage in the Muslim world—a trend to which our own actions have contributed. The enduring threat is not Osama bin Laden but young Muslims with no jobs and no hope, who are angry with their own governments and increasingly see the United States as an enemy of Islam” (Kean & Hamilton, 2007, p. B1). As this assessment indicates, structural conditions do not justify terrorism, of course, but they do help explain why some individuals decide to commit it.
THE IMPACT OF TERRORISM
The major impact of terrorism is apparent from its definition, which emphasizes public fear and intimidation. Terrorism can work, or so terrorists believe, precisely because it instills fear and intimidation. Anyone who might have happened to be in or near New York City on 9/11 will always remember how terrified the local populace was to hear of the attacks and the fears that remained with them for the days and weeks that followed.

Hardly anyone likes standing in the long airport security lines that are a result of the 9/11 attacks. Some experts say that certain airport security measures are an unneeded response to these attacks.
Another significant impact of terrorism is the response to it. As mentioned earlier, the 9/11 attacks led the United States to develop an immense national security network that defies description and expense, as well as the Patriot Act and other measures that some say threaten civil liberties; to start the wars in Iraq and Afghanistan; and to spend more than $3 trillion in just one decade on homeland security and the war against terrorism. Airport security increased, and Americans have grown accustomed to having to take off their shoes, display their liquids and gels in containers limited to three ounces, and stand in long security lines as they try to catch their planes.
People critical of these effects say that the “terrorists won,” and, for better or worse, they may be correct. As one columnist wrote on the tenth anniversary of 9/11, “And yet, 10 years after 9/11, it’s clear that the ‘war on terror’ was far too narrow a prism through which to see the planet. And the price we paid to fight it was far too high” (Applebaum, 2011, p. A17). In this columnist’s opinion, the war on terror imposed huge domestic costs on the United States; it diverted US attention away from important issues regarding China, Latin America, and Africa; it aligned the United States with authoritarian regimes in the Middle East even though their authoritarianism helps inspire Islamic terrorism; and it diverted attention away from the need to invest in the American infrastructure: schools, roads, bridges, and medical and other research. In short, the columnist concluded, “in making Islamic terrorism our central priority—at times our only priority—we ignored the economic, environmental and political concerns of the rest of the globe. Worse, we pushed aside our economic, environmental and political problems until they became too great to be ignored” (Applebaum, 2011, p. A17).
To critics like this columnist, the threat to Americans of terrorism is “over-hyped” (Holland, 2011b). They acknowledge the 9/11 tragedy and the real fears of Americans, but they also point out that in the years since 9/11, the number of Americans killed in car accidents, by air pollution, by homicide, or even by dog bites or lightning strikes has greatly exceeded the number of Americans killed by terrorism. They add that the threat is overhyped because defense industry lobbyists profit from overhyping it and because politicians do not wish to be seen as “weak on terror.” And they also worry that the war on terror has been motivated by and also contributed to prejudice against Muslims (Kurzman, 2011).
|
Learning Objective: Key Takeaways |
|
|
Learning Objective: For Your Review |
|
THE USA PATRIOT ACT [175]
After the 9/11 terrorist attack in 2001, Congress passed the USA Patriot Act. The U.S. Department of Justice’s website has a page entitled Preserving Life & Liberty. (https://www.justice.gov/archive/ll/highlights.htm) The top of that page states the following regarding the Patriot Act.
The Department of Justice’s first priority is to prevent future terrorist attacks. Since its passage following the September 11, 2001 attacks, the Patriot Act has played a key part – and often the leading role – in a number of successful operations to protect innocent Americans from the deadly plans of terrorists dedicated to destroying America and our way of life. While the results have been important, in passing the Patriot Act, Congress provided for only modest, incremental changes in the law. Congress simply took existing legal principles and retrofitted them to preserve the lives and liberty of the American people from the challenges posed by a global terrorist network.
Congress enacted the Patriot Act by overwhelming, bipartisan margins, arming law enforcement with new tools to detect and prevent terrorism: The USA Patriot Act was passed nearly unanimously by the Senate 98-1, and 357-66 in the House, with the support of members from across the political spectrum.
The Act Improves Our Counter-Terrorism Efforts in Several Significant Ways:
- The Patriot Act:
- allows investigators to use the tools that were already available to investigate organized crime and drug trafficking. Many of the tools the Act provides to law enforcement to fight terrorism have been used for decades to fight organized crime and drug dealers and have been reviewed and approved by the courts. As Sen. Joe Biden (D-DE) explained during the floor debate about the Act, “the FBI could get a wiretap to investigate the mafia, but they could not get one to investigate terrorists. To put it bluntly, that was crazy! What’s good for the mob should be good for terrorists.” (Cong. Rec., 10/25/01)
- allows law enforcement to use surveillance against more crimes of terror. Before the Patriot Act, courts could permit law enforcement to conduct electronic surveillance to investigate many ordinary, non-terrorism crimes, such as drug crimes, mail fraud, and passport fraud. Agents also could obtain wiretaps to investigate some, but not all, of the crimes that terrorists often commit. The Act enabled investigators to gather information when looking into the full range of terrorism-related crimes, including chemical-weapons offenses, the use of weapons of mass destruction, killing Americans abroad, and terrorism financing.
- allows federal agents to follow sophisticated terrorists trained to evade detection. For years, law enforcement has been able to use “roving wiretaps” to investigate ordinary crimes, including drug offenses and racketeering. A roving wiretap can be authorized by a federal judge to apply to a particular suspect, rather than a particular phone or communications device. Because international terrorists are sophisticated and trained to thwart surveillance by rapidly changing locations and communication devices such as cell phones, the Act authorized agents to seek court permission to use the same techniques in national security investigations to track terrorists.
- allows law enforcement to conduct investigations without tipping off terrorists. In some cases, if criminals are tipped off too early to an investigation, they might flee, destroy evidence, intimidate or kill witnesses, cut off contact with associates, or take other action to evade arrest. Therefore, federal courts in narrow circumstances long have allowed law enforcement to delay for a limited time when the subject is told that a judicially approved search warrant has been executed. Notice is always provided, but the reasonable delay gives law enforcement time to identify the criminal’s associates, eliminate immediate threats to our communities, and coordinate the arrests of multiple individuals without tipping them off beforehand. These delayed notification search warrants have been used for decades, have proven crucial in drug and organized crime cases, and have been upheld by courts as fully constitutional.
- allows federal agents to ask a court for an order to obtain business records in national security terrorism cases. Examining business records often provides the key that investigators are looking for to solve a wide range of crimes. Investigators might seek select records from hardware stores or chemical plants, for example, to find out who bought materials to make a bomb, or bank records to see who’s sending money to terrorists. Law enforcement authorities have always been able to obtain business records in criminal cases through grand jury subpoenas and continue to do so in national security cases where appropriate. These records were sought in criminal cases such as the investigation of the Zodiac gunman, where police suspected the gunman was inspired by a Scottish occult poet and wanted to learn who had checked the poet’s books out of the library. In national security cases where use of the grand jury process was not appropriate, investigators previously had limited tools at their disposal to obtain certain business records. Under the Patriot Act, the government can now ask a federal court (the Foreign Intelligence Surveillance Court), if needed to aid an investigation, to order production of the same type of records available through grand jury subpoenas. This federal court, however, can issue these orders only after the government demonstrates the records concerned are sought for an authorized investigation to obtain foreign intelligence information not concerning a U.S. person or to protect against international terrorism or clandestine intelligence activities, provided that such investigation of a U.S. person is not conducted solely on the basis of activities protected by the First Amendment.
- The Patriot Act facilitated information sharing and cooperation among government agencies so that they can better “connect the dots.” The Act removed the major legal barriers that prevented the law enforcement, intelligence, and national defense communities from talking and coordinating their work to protect the American people and our national security. The government’s prevention efforts should not be restricted by boxes on an organizational chart. Now police officers, FBI agents, federal prosecutors and intelligence officials can protect our communities by “connecting the dots” to uncover terrorist plots before they are completed. As Sen. John Edwards (D-N.C.) said about the Patriot Act, “we simply cannot prevail in the battle against terrorism if the right hand of our government has no idea what the left hand is doing” (Press release, 10/26/01) Prosecutors and investigators used information shared pursuant to section 218 in investigating the defendants in the so-called “Virginia Jihad” case. This prosecution involved members of the Dar al-Arqam Islamic Center, who trained for jihad in Northern Virginia by participating in paintball and paramilitary training, including eight individuals who traveled to terrorist training camps in Pakistan or Afghanistan between 1999 and 2001. These individuals are associates of a violent Islamic extremist group known as Lashkar-e-Taiba (LET), which operates in Pakistan and Kashmir, and that has ties to the al Qaeda terrorist network. As the result of an investigation that included the use of information obtained through FISA, prosecutors were able to bring charges against these individuals. Six of the defendants have pleaded guilty, and three were convicted in March 2004 of charges including conspiracy to levy war against the United States and conspiracy to provide material support to the Taliban. These nine defendants received sentences ranging from a prison term of four years to life imprisonment.
- The Patriot Act:
- updated the law to reflect new technologies and new threats. The Act brought the law up to date with current technology, so we no longer have to fight a digital-age battle with antique weapons-legal authorities leftover from the era of rotary telephones. When investigating the murder of Wall Street Journal reporter Daniel Pearl, for example, law enforcement used one of the Act’s new authorities to use high-tech means to identify and locate some of the killers.
- allows law enforcement officials to obtain a search warrant anywhere a terrorist-related activity occurred. Before the Patriot Act, law enforcement personnel were required to obtain a search warrant in the district where they intended to conduct a search. However, modern terrorism investigations often span a number of districts, and officers therefore had to obtain multiple warrants in multiple jurisdictions, creating unnecessary delays. The Act provides that warrants can be obtained in any district in which terrorism-related activities occurred, regardless of where they will be executed. This provision does not change the standards governing the availability of a search warrant but streamlines the search-warrant process.
- allows victims of computer hacking to request law enforcement assistance in monitoring the “trespassers” on their computers. This change made the law technology-neutral; it placed electronic trespassers on the same footing as physical trespassers. Now, hacking victims can seek law enforcement assistance to combat hackers, just as burglary victims have been able to invite officers into their homes to catch burglars.
- The Patriot Act:
- increased the penalties for those who commit terrorist crimes. Americans are threatened as much by the terrorist who pays for a bomb as by the one who pushes the button. That’s why the Patriot Act imposed tough new penalties on those who commit and support terrorist operations, both at home and abroad.
- prohibits the harboring of terrorists. The Act created a new offense that prohibits knowingly harboring persons who have committed or are about to commit a variety of terrorist offenses, such as: destruction of aircraft; use of nuclear, chemical, or biological weapons; use of weapons of mass destruction; bombing of government property; sabotage of nuclear facilities; and aircraft piracy.
- enhanced the inadequate maximum penalties for various crimes likely to be committed by terrorists: including arson, destruction of energy facilities, material support to terrorists and terrorist organizations, and destruction of national-defense materials.
- enhanced a number of conspiracy penalties, including for arson, killings in federal facilities, attacking communications systems, material support to terrorists, sabotage of nuclear facilities, and interference with flight crew members. Under previous law, many terrorism statutes did not specifically prohibit engaging in conspiracies to commit the underlying offenses. In such cases, the government could only bring prosecutions under the general federal conspiracy provision, which carries a maximum penalty of only five years in prison.
- punishes terrorist attacks on mass transit systems.
- punishes bioterrorists.
- eliminates the statutes of limitations for certain terrorism crimes and lengthens them for other terrorist crimes.
The government’s success in preventing another catastrophic attack on the American homeland since September 11, 2001, would have been much more difficult, if not impossible, without the USA Patriot Act. The authorities Congress provided have substantially enhanced our ability to prevent, investigate, and prosecute acts of terror.
CYBER CRIME [176]
TYPES OF CYBERCRIME
Crime has evolved with the advancements of the internet and social media. The parallel between technology and the types of crimes that are committed is astonishing. As technology became more readily available to the masses, the types of crimes committed shifted over time. A clear distinction has been formed based on the involvement of cybertechnology in crime. Crimes that would not exist or be possible without the existence of cybertechnology are true Cybercrimes. To be most accurate, these crimes can be classified as cyberspecific crimes. Crimes that can be committed that do not necessarily need cybertechnology to be possible, but are made easier by its existence, are known as cyber-related crimes. Of Cyber-related crimes, there are two distinct categories that can be identified. The first are Cyber-assisted crimes. These are crimes in which cybertechnology is simply used to aid a crime, such as committing tax fraud or being assaulted with a computer. The other category is known as Cyberexacerbated crimes, which are crimes that have increased significantly due to cybertechnology.
CYBER-ASSISTED CRIMES
Cyber-assisted crimes are the most basic crimes that can be committed with the use of cybertechnology. Put simply, these are essentially normal crimes that have occurred throughout time on a regular basis. The only difference is that cybertechnology has played some small part in the crime. Property damage, for example, is one kind of cyber-assisted crime. If someone destroys your computer or cellphone, it constitutes as property damage but can also be classified as a cyber-assisted crime. Similarly, if you are assaulted with a phone, printer, computer or other device, the attack constitutes as assault but can also be classified as a Cyber-assisted crime.
The most common type of cyber-assisted crime that you will see is fraud. Fraud typically is a crime that does not require much thought to actually commit. As a crime, it has always been relatively easy to commit. With the use of cybertechnology, it only becomes much easier to actually carry out from start to finish.
CYBEREXACERBATED CRIMES
Cyberexacerbated crimes are a type of cyber-related crime, but they are much worse than cyber-assisted crimes. These crimes have increased significantly due to cybertechnology. Most crimes have evolved to maintain their own categories due to the sheer volume of crimes and their slight uniqueness due to their ease with the use of cybertechnology.
Cyberbullying is defined as the “intentional and repeated harm inflicted on people through the use of computers, cellular telephones, and other electronic devices.” Previously something that happened offline only, cyberbullying is a huge crime that leads to victims suffering from low self-esteem, depression, and sometimes even driving them to commit suicide. With the use of the internet, it is possible for people to receive thousands of hateful comments from individuals at a single time.
Cyberstalking is exactly what one would think, except occurring in a digital space. Cybertechnology allows for criminals to keep tabs on people, watching all of their online activity and making it very uncomfortable for victims to even want to utilize things such as their own personal social media. Perhaps the most disconcerting thing is that the perpetrator can always be online.
Internet pedophilia and pornography are some of the more disturbing cyberexacerbated crimes. Due to the ability for communities of like-minded individuals to be easily formed online, pedophiles are able to form online communities and facilitate the creation and dissemination of child pornography.
CYBERSPECIFIC CRIMES
Cyberspecific crimes do not exist without the internet as we know it. Because of that, these are the most unique cybercrimes and could be considered as the only “true” cybercrimes. Cybertrespassing is one of these crimes. At its core, cybertrespassing takes its roots from actual trespassing. Essentially, perpetrators gain access to stores of information that they otherwise should not have access to because of the lack of permissions. The reason why this is so dangerous is because it opens the door for cybertrespassing to easily become a data breach if information is taken.
Cybervandalism is another form cyberspecific crime. Taking its roots from actual vandalism, cybervandalism began harmlessly with the defacing of websites on the internet. While annoying, it didn’t necessarily present any damage. It wasn’t until cyberattacks with the intent of harming computers were created that cybervandalism became a huge issue.
TYPES OF CYBER ATTACKS
Viruses are pieces of computer programming code that causes a computer to behave in an undesirable way. Viruses can be attached to files or stored in the computer’s memory. Viruses may be programmed to different things such when they are downloaded or activated by a specific action for example viruses attached to file will infect that computer and any file created or modified on that machine. Viruses may also have programmed to display a message when certain activities are performed to execute the virus. Worms like viruses bury themselves in the memory of a machine and then duplicates itself with help from any help. It can send itself through emails and other connections. Phishing is when hackers try to obtain financial or other confidential information from Internet users, typically by sending an e-mail that looks as if it is from a legitimate organization, usually a financial institution, but contains a link to a fake Web site that replicates the real one. These con - artists urge the recipient of such emails to take action for rewards or avoid consequences. Hackers may use a backdoor within a computer system that is vulnerable, this allows them to remain undetected while they access important information. Key-logger programs allow attackers to view information that has been logged into a particular machine undetected. Botnets are a collection of computers that could be spread around the world; they are connected to the internet and controlled by one single computer.
Summary
As the 21 st century progresses, technology and crime will continue to become more closely linked; technology is changing the face of crime and policing is adapting as a result. Yet many of the core motivations behind policing and the philosophies utilized in making policing policies will continue to shape the field of law and law enforcement. Technology and goals may shift but good policework is derived from self-awareness, emotional intelligence, community consciousness, and adaptability.