13.3: Where Are Vulnerabilities? Understanding the Weaknesses
- Page ID
- 4584
\( \newcommand{\vecs}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \) \( \newcommand{\vecd}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash {#1}}} \)\(\newcommand{\id}{\mathrm{id}}\) \( \newcommand{\Span}{\mathrm{span}}\) \( \newcommand{\kernel}{\mathrm{null}\,}\) \( \newcommand{\range}{\mathrm{range}\,}\) \( \newcommand{\RealPart}{\mathrm{Re}}\) \( \newcommand{\ImaginaryPart}{\mathrm{Im}}\) \( \newcommand{\Argument}{\mathrm{Arg}}\) \( \newcommand{\norm}[1]{\| #1 \|}\) \( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\) \( \newcommand{\Span}{\mathrm{span}}\) \(\newcommand{\id}{\mathrm{id}}\) \( \newcommand{\Span}{\mathrm{span}}\) \( \newcommand{\kernel}{\mathrm{null}\,}\) \( \newcommand{\range}{\mathrm{range}\,}\) \( \newcommand{\RealPart}{\mathrm{Re}}\) \( \newcommand{\ImaginaryPart}{\mathrm{Im}}\) \( \newcommand{\Argument}{\mathrm{Arg}}\) \( \newcommand{\norm}[1]{\| #1 \|}\) \( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\) \( \newcommand{\Span}{\mathrm{span}}\)\(\newcommand{\AA}{\unicode[.8,0]{x212B}}\)
Learning Objectives
After studying this section you should be able to do the following:
- Recognize the potential entry points for security compromise.
- Understand infiltration techniques such as social engineering, phishing, malware, Web site compromises (such as SQL injection), and more.
- Identify various methods and techniques to thwart infiltration.
Figure 13.1
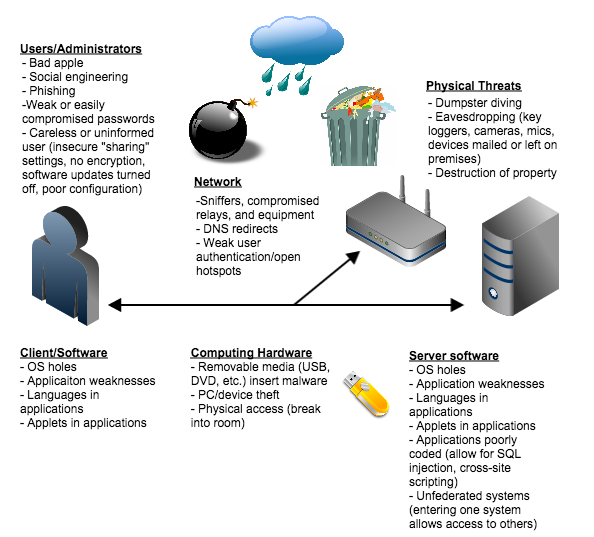
This diagram shows only some of the potential weaknesses that can compromise the security of an organization’s information systems. Every physical or network “touch point” is a potential vulnerability. Understanding where weaknesses may exist is a vital step toward improved security.
Modern information systems have lots of interrelated components and if one of these components fails, there might be a way in to the goodies. This creates a large attack surface for potential infiltration and compromise, as well as one that is simply vulnerable to unintentional damage and disruption.


