13.7: Mitigating and Managing Risks
- Page ID
- 51121
By the end of this section, you will be able to:
- Explain Enterprise Risk Management and how a company uses it
- Describe litigation and financial risks
- Describe common insurance needs
Risk management is key to operating any business in a profitable fashion. There are many risks facing an entrepreneur when starting and operating a new business venture. The trick is to eliminate risks that will hurt the venture, while taking on risks that will provide for long-term profitability. The risks facing the entrepreneur need to be initially identified as part of developing a business plan and revisited regularly in ongoing operations. Preparation for adverse events affecting a new business venture is necessary, but being too pessimistic or allowing fear of adverse events to stop an entrepreneur from taking any risk will keep a business venture from achieving it greatest potential and profit.
It is important that an entrepreneur develop an understanding of the risks of the business environment. The risks include liability risks stemming from contracts and torts, sometimes referred to as operating risks, regulatory compliance risks, financial risks, and strategic risks, including taxation. Understanding how the business structure is used to operate the business venture allows the entrepreneur to develop a plan to manage business growth and understand business risk.
Enterprise Risk Management
Profitable ventures develop a strong enterprise risk management program, which is an integrated, cross-disciplinary approach to monitoring risk. An organization needs to look at both long-term and short-term risks at all levels of the organization, and these risks need to be evaluated from all stakeholders’ perspectives and developed into an entity-wide program.
Enterprise risk management attempts to address the specific risks discussed in the preceding section by implementing a risk program that enables a business to identify and manage risk. Specifically, a business will go through a process that involves a multistage process of risk identification, risk assessment, and risk abatement. Examples of risks that businesses face include those from natural causes, economic causes, and human causes.
Natural causes of risk include disasters such as hurricanes and flooding, as well as earthquakes or other catastrophes that result in loss of life and property, as well as business interruption. For example, a business in New Orleans could be flooded by a hurricane. This results in damage to facilities and products, and threatens the lives of workers. In order to counter such causes, businesses need to plan ahead for business continuity, take out comprehensive insurance coverage, and have an evacuation/shut-down plan in place.
Economic causes of risk include global events leading to rising prices of raw materials, currency fluctuation, high interest rates, and, of course, competition from other companies in the same industry. An example of this would be unpredictable trade wars with China, leading to tariffs.
Human causes of risk refer to actions by employees, contractors, and those persons over which a company has control. These events can include torts stemming from negligence at work, labor strikes, shortages of qualified trained workers, and corporate mismanagement. An example of this type of risk would include embezzlement of money by an internal financial executive.
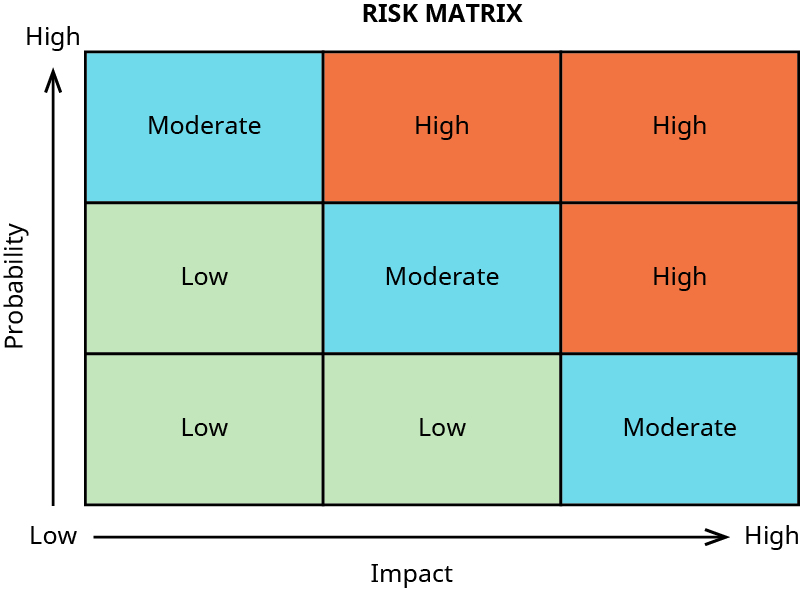
The use of a comprehensive approach allows a business entity to review and combine all risks into a functional perspective that allows the entrepreneur to evaluate risks and integrate new risks as different opportunities become more important to the business venture. Businesses sometimes use a risk matrix to assess or characterize the probability and impact of risk (Figure 13.11). The use of such a tool can help a business quantify risk and decide whether to undertake an activity based on its level of risk.
Risk appetite is important for a business venture to consider, both when creating its business structure and during ongoing operations. Table 13.1 shows an overview of the considerations a business venture should entertain in both its creation and operation.
| Risk Item | Consideration |
|---|---|
| Existing risk profile | Current level and distribution of risks across the business and across risk categories |
| Risk capacity | Amount of risk the business can support while pursuing its objectives |
| Risk tolerance | Amount of variation the business can tolerate while pursuing its objectives |
| Risk attitude | Management’s attitudes toward growth, risk, and return |
COSO’s Enterprise Risk Management, Understanding and Communicating Risk Appetite outlines these considerations for assessing a business’s appetite for risk.
This is the basic approach to evaluating a new venture’s appetite for risk. Determining and understanding the risks facing a new venture should start during the preparation of the business venture’s written business plan and should continue through the operations of the venture.
The Committee of Sponsoring Organizations of the Treadway Commission, also known as COSO, deals with risk management. The mission statement of the COSO is “to provide thought leadership through the development of comprehensive frameworks and guidance on enterprise risk management, internal control and fraud deterrence designed to improve organizational performance and governance and to reduce the extent of fraud in organizations.”
Legal Risk and Protection
Business operations of any sort need to follow business regulations and laws. The failure to follow business regulations may lead to fines, lawsuits, or even criminal penalties. Legal risk stems primarily from a breach of contract and/or the commission of a tort. Common examples of this type of risk includes product liability lawsuits. These lawsuits are frequently very expensive class action lawsuits or regulatory investigations of dangerous products. There are many famous case examples including automobiles, asbestos, pharmaceutical drugs, breast implants, and airplanes.
Other lawsuits stem from contracts, including borrowing money from a bank. The business has an obligation to pay it back, or it breaches a covenant within a contract. Other common types of contracts are those used in selling services and products, leasing real estate, and other similar contractual obligations.
Due to liability risks, business owners and investors are always looking for ways to limit their personal liability. Incorporation is a standard risk protection strategy for this potential problem, as are the use of other types of limited liability structures such as LLCs. This is one of the main advantages of properly operated corporations and LLCs, which allow for limited personal liability of owners and investors. Partners in GPs and sole proprietors are personally liable for all of the debts of the business, even beyond their own investment in the business.
However, a particular challenge for small business entrepreneurs is that even when they form a corporation or LLC, many lenders, landlords, and other entities providing credit to a small business circumvent the limited liability protection by requiring owners and investors to personally guarantee the debts of the business operations. This means that the owner who personally guarantees the credit will have to pay back the obligation if the business cannot. An owner can obtain insurance or borrow money for such guarantees. LLCs and corporations do protect their owners, shareholders, and members from a number of different tort claims, such as personal injury lawsuits and claims made directly against the organization.
Financial Risk and Protection
An entrepreneur needs money to launch a business, whether that comes in the form of loans from family, their own savings, or investors. The founder will be expected to put their own money at risk, whether in the form of a loan to their own business or equity in their own business. If they do not have any “skin in the game,” then others will not be interested in loaning them money. This means that if the business fails, it will have repercussions for the owner, even if they operate as a corporation or LLC. This is the essence of financial risk: starting a new business with insufficient funds to sustain operations over an extended period of time.
Any new business owner needs to have a sound financial strategy as a part of the overall business plan. This should show income projections, the liquid assets that will be required to break even, and the expected return on investment for all investors in the first five-to-ten-year timeframe. Failure to accurately plan could mean that the entrepreneur risks business closure and bankruptcy, and investors get nothing.
Insurance Protection
Risk management and protection are enhanced with the purchase of different types of insurance, which involves spreading risk over a large number of people (policyholders). If a company is a corporation, it may need directors’ and officers’ liability insurance to indemnify the directors and officers if they get sued. Another insurance policy many companies get is called errors and omissions insurance, and this insurance coverage protects employees in negligence claims and cases if employee theft. Other types of insurance policies that most businesses carry include automobile insurance, health insurance, property insurance, and cyber/data breach insurance. Insurance coverage for a business venture needs to be specific to the business structure and its operations. Keep in mind that not all risks can be insured against—for example, a bad economy that leads to a loss of business or a bad decision by the owner to enter a market that does not work out.
Information Technology/Cybersecurity for Small Businesses
According to the SBA, the risk of hacking, ransomware, and customer privacy are equally as significant for most small businesses as for larger ones. The SBA has set guidelines related to cybersecurity for entrepreneurs. The SBA recommends the ten-step action plan shown in Table 13.2.
| Step | Action |
|---|---|
| 1 | Protect against viruses, spyware, and other malicious code |
| 2 | Secure your networks |
| 3 | Establish security practices and policies to protect sensitive information |
| 4 | Educate employees about cyber threats and hold them accountable |
| 5 | Require employees to use strong passwords and change them often |
| 6 | Employ best practices on payment cards |
| 7 | Make backup copies of important business data and information |
| 8 | Control physical access to computers and network components |
| 9 | Create a mobile device action plan |
| 10 | Protect all pages on your public-facing websites and apps, not just the checkout and sign-up pages |
The Federal Communications Commission joins the SBA in the preceding recommendations. For more information, see the following website: https://www.fcc.gov/general/cybersec...small-business.
Managing Payment Data
If you operate a small business, are you prepared to deal with hackers who break into your website and steal credit card data from consumers who bought your products online? Small businesses running an e-commerce site must comply with the Payment Card Industry Data Security Standard (https://www.pcisecuritystandards.org/). This is a regulation that could cause severe legal risk for entrepreneurs if your system is compromised, and credit card data are stolen. Consumers rightfully expect and demand a safe online experience when they visit your site. Have you paid an expert to evaluate your system and install the best security system? It may be costly, but perhaps not as expensive as the damages you could be ordered to pay by a court if credit card data are hacked.